One-time Microsoft 365 project deployment.
One-time Microsoft 365 project deployment.
One-time Microsoft 365 project deployment.
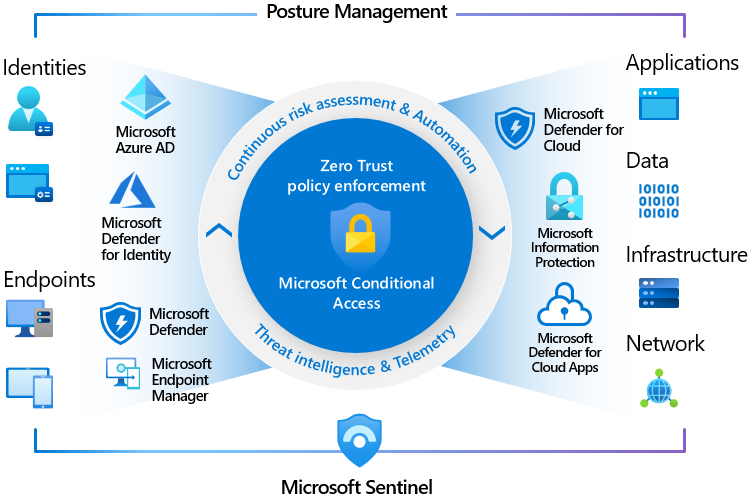
Zero Trust is a modern security strategy we incorporate in our managed modern workplace services. It is based on the principle never trust, always verify, and assume breach. Instead of assuming everything behind the corporate firewall is safe, the Zero Trust model assumes breach and verifies each request as though it originates from an open network.
Always authenticate and authorize based on all available data points, including user identity, location, device health, service or workload, data classification, and anomalies.
We limit user access with just-in-time and just-enough-access, risk-based adaptive polices, and data protection to help secure data and improve productivity.
All services are only available from compliant devices that are verified secure, we use analytics to gain visibility into possible malicious behavior and leverage several techniques to scan for threats and possible breaches.
Add Your Heading Text HLeveraging our platform, we manage, monitor and proactively remediate issues in your entire environment.ere
We ensure proper functionality of Microsoft 365 email delivery using email analytic and compliance tools. And ensure all devices and users are secured by the highest level of security, compliant with all major security frameworks.
Managed third-party application updates improve user experience, but also ensure a safer work environment. We auto-update applications where possible, and notify users when manual action is needed.
Backup rules recommend a 3-2-1 backup strategy, 3 copies of all data, stored on 2 different media, and one copy off-site. This ensures business continuity in worst case scenarios.

Our advanced phishing detection works on any device, for all users, and protects against modern Man In The Middle phishing attacks, which regular MFA does not protect against. Phish login demo is shown in the video, confirmed by the red background. This check is performed each time a user signs in, regardless of the device that is used.
We match Microsoft 365 activity with threat intelligence, containing malicious IP addresses and bot network info.
We monitor for suspicious Microsoft 365 account activity that could indicate compromises. This includes, for example, Outlook Inbox rule creation, indicating possible invoice fraud scams after user compromises.
Our custom automation engine isolates users and devices during high-severity incidents. Ensuring threats and threat actors are unable to move lateral throughout the organization or to customers.
Continuous 24/7 monitoring of the Dark Web for domains, credentials, IP addresses, and email addresses alerts us to any breaches, indicating compromises in internal or third-party systems. This proactive approach enables us to take action before threat actors can exploit this intelligence.

Work on a virtual desktop, dynamically scalable, pay per
We specialize in Azure Virtual Desktop Environments and can easily manage and deploy a full AVD environment in a short time span. Our Intune environment already contains all best practices and is ready to manage AVD Hosts, eliminating the need for expensive hosted infrastructure.
Pay only for what you use, auto-scale up and down when users sign in.
Managed with Entra and Intune, leveraging enterprise state roaming, results in an identical copy of your local managed device.
Extremely useful for publishing legacy applications that require a backend server.
Optional GPUs allow graphical designers to work from anywhere without high-end hardware. Auto-scaling keeps the costs low.


Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis leo.