Malware Analysis – Shortcuts in zip file
Recently, we encountered two distinct variants of a payload delivered through Google Drive, both containing a malicious shortcut. While these threats were successfully mitigated, it’s crucial to understand their mechanisms and implement protective measures. In this blog, we’ll dissect these threats and explore strategies for defending against them. Threat Analysis The malicious shortcuts in the […]
Automating Azure SQL Maintenance with Azure Automation
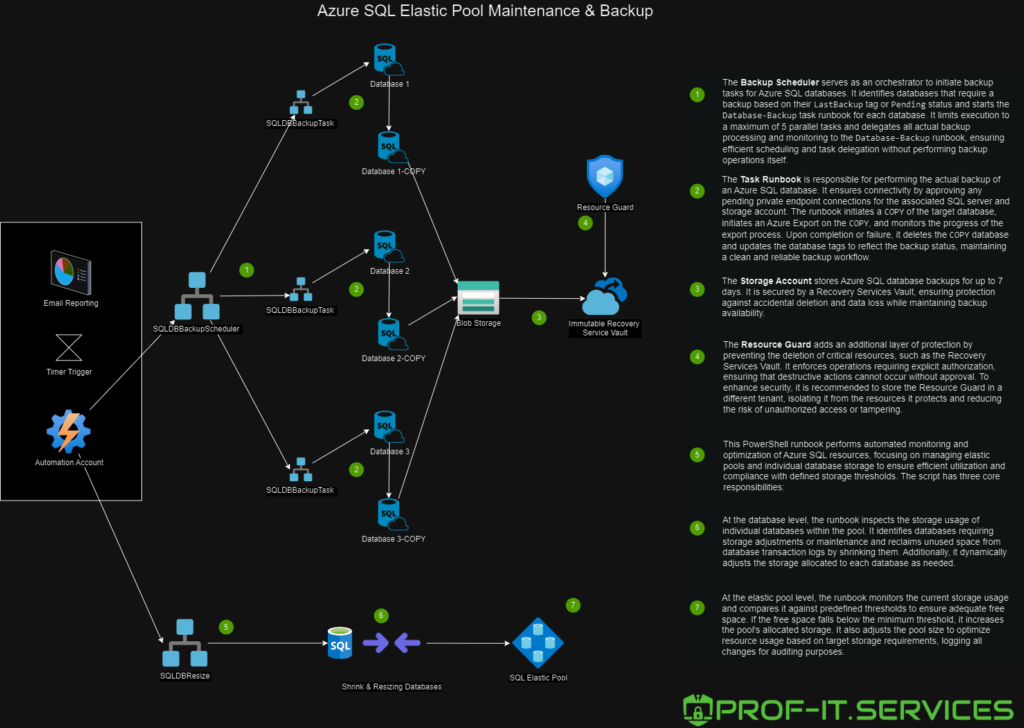
Keeping Your Azure SQL Databases Healthy: The Power of Automation In the realm of database management, maintaining optimal performance and storage efficiency for your Azure SQL Elastic pool and databases is critical. SQL databases are the backbone of countless business applications, supporting everything from transaction processing to analytics. However, as they grow over time, they […]
Platform Upgrade: Microsoft 365 agentless CSS phishing protection
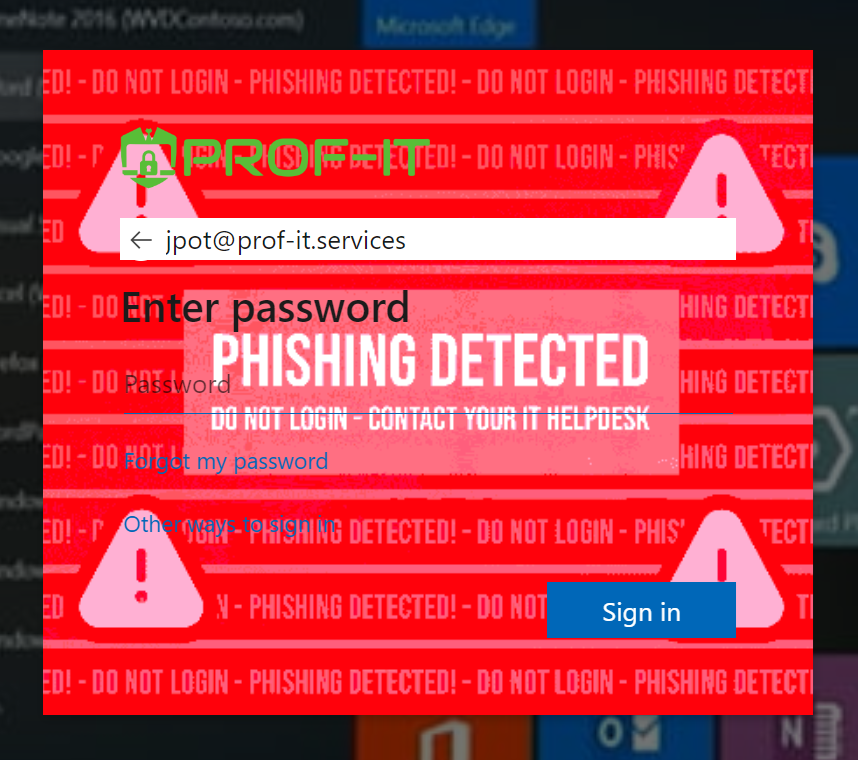
Exciting news! 🎉 We’ve recently created this advanced CSS phishing protection, and we’re making it available for everyone, for free! Using custom CSS and a server-side solution, we can swiftly detect Man-in-the-middle (MITM) Phishing attacks, which MFA does not protect against. During each login, servers validate the login session, and users are alerted by a […]
EntraIDMicrosoft 365Modern WorkplaceSecurity

By creating unmanaged Google accounts using your corporate domain (e.g., name@yourcompany.com), users or attackers can exploit a significant security loophole to bypass Microsoft 365 Conditional Access (CA) policies. These unmanaged accounts are not governed by your organization’s security controls, such as multifactor authentication (MFA), device compliance checks, or geolocation restrictions. As a result, anyone can log […]
